SaaS is being embraced by businesses of all sizes due to its increased productivity and efficiency. However, SaaS applications and services considerably amplify the security difficulties. Organizations of all types face a far larger risk of data breaches without the safety net of secure on-premise networks and devices. And data breaches are expensive, both monetarily and in terms of reputation. Without the safety net of restricted data access, secure networks, and protected devices, how can SaaS apps be secured? One of the biggest problems that organizations must solve is this.
This article explores the security issues that SaaS applications face before outlining the best practices for securing SaaS applications.
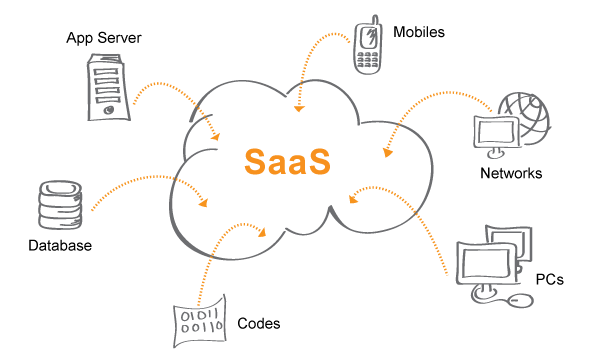
What Is SaaS Security?
Software-as-a-service (SaaS) environments are a particularly attractive target for cybercriminals because they tend to store a large variety and amount of sensitive data, including payment card details and personally identifiable information. Thus, it is crucial for companies to prioritize SaaS security.
SaaS security covers a range of practices that organizations implement to protect their assets when using a SaaS architecture. According to the UK’s National Cyber Security Centre (NCSC) SaaS security guidelines, responsibility for security is shared between the customer and the service provider or software distributor. Additionally, vendors are introducing SaaS Security Posture Management (SSPM) systems that can regulate and automate SaaS security.
Many organizations are well-experienced in handling the security risks associated with Infrastructure-as-a-Service (IaaS) and Platform-as-a-Service (PaaS) environments. IT and security teams typically collaborate using integrated business processes and programs. There is also a large market for IaaS and PaaS security and management tools.
SaaS applications tend to operate differently and offer advantages for organizations. However, they can be harder to manage in terms of security:
- Complexity—SaaS apps are designed to serve a wide variety of teams across an organization. For example, record systems are used by sales teams for customer data, by development teams for source code, and human resource teams for HR information. Such SaaS applications tend to be used frequently by multiple end-users who may have different levels of technical knowledge. The sheer volume and complexity of usage makes SaaS applications difficult for security teams to understand.
- Communication—security teams have little communication with the business administrators who select and manage new SaaS technologies. The limited interaction between teams makes it harder for security teams to understand the scope of use and the associated threats to the organization when these applications become fully operational.
- Collaboration—internal teams supporting SaaS applications tend to focus on functionality and business requirements, often lacking the necessary guidance to secure them. Balancing business and security needs requires collaboration on an ongoing basis. To ensure consistency, organizations should focus more resources and effort on identifying and addressing security risks, and treat SaaS with the same respect as bare metal, IaaS, PaaS, and endpoint security.
Challenges in Securing SaaS Platforms
The increasing adoption of Software as a Service (SaaS) solutions by businesses has brought new security concerns for IT teams. Key challenges in securing SaaS platforms include:
1. Fragmented Platforms and Applications
SaaS ecosystems often consist of multiple applications and services originating from various vendors. This fragmentation makes it challenging to implement and maintain a unified security approach, potentially leading to gaps in defense and difficulties in monitoring threats across all platforms. Multiple high profile data breaches have demonstrated that cybercriminals are quick to exploit these weaknesses.
2. Intricate Custom Configurations
SaaS platforms provide organizations with the flexibility to adapt their configurations to meet specific requirements. However, this customization can also add complexity to the environment and raise the likelihood of misconfigurations or insecure settings being overlooked. In recent years, misconfigured cloud servers have become a primary cause of data breaches.
3. Evolving Environments and User Access
In SaaS environments, users can access applications from various devices and locations at any given time. Balancing secure access with user productivity is a demanding task for IT security teams, who must manage ever-changing user roles, permissions, and authentication requirements without compromising security measures.
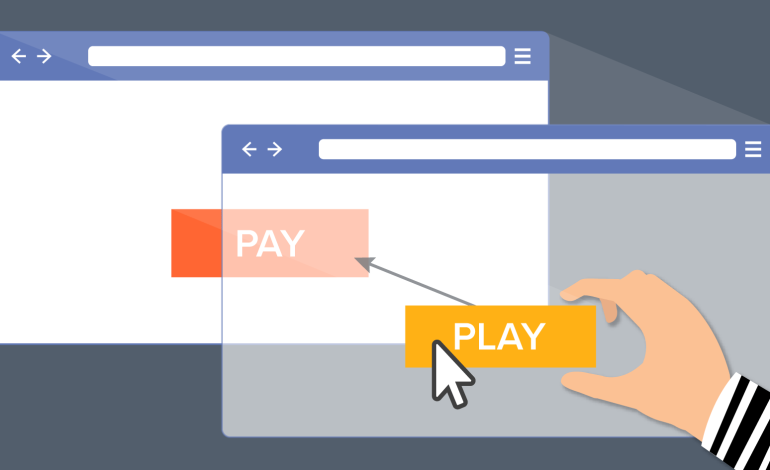
4. Shadow IT and Personal Devices
Employees may install and utilize unauthorized SaaS applications without the consent or awareness of IT teams, resulting in a phenomenon known as shadow IT. These unsanctioned apps can introduce security threats, such as data leakage or malware infections. Managing shadow IT is an enduring challenge for organizations seeking to maintain control over their SaaS environment.
Read Also: How do You Deploy SaaS?
In addition, SaaS applications are commonly used by employees on personal devices or via unsecured networks, creating additional security risks.
How to Secure SaaS Applications?
1. Vetting, Continuous Monitoring, and Audits of SaaS Vendors
One of the critical ways to face the challenge of ‘how to secure SaaS applications’ in the present and the future is by choosing your SaaS providers carefully. Take your time to vet the vendor, understand the security mechanisms and controls, and rigorously and thoroughly. Do not compromise on compliance certifications such as PCI-DSS, GDPR, etc. These certifications tell you that the SaaS provider is invested in security.
But do not stop with the one-time vetting of SaaS providers. Continuously monitor and regularly audit to ensure they maintain the highest security standards amid the rapid changes.
2. Secure Product Engineering and Development
Secure product engineering and development help you address the ‘how to secure SaaS applications?’ at a much earlier stage. By baking security into the SDLC stages, you will be able to detect and fix vulnerabilities and misconfigurations before they spiral into bigger challenges in production. You can ensure security by design through secure coding and secure components in your SaaS-based applications.
3. Stronger Authentication
As organizations leverage and deploy more SaaS apps, login credentials are lucrative targets for attackers, and passwords are insufficient to authenticate users. More robust authentication measures, including strong passwords, multi-factor authentication, single sign-on, etc., are necessary.
4. Monitor and Update the Inventory
One of the important aspects of SaaS-based applications is the ability to deploy them rapidly. This agility leads to new, unexpected usage. This needs to be closely monitored and documented using manual data gathering methods and automated tools. The new usage is to be added to a reliable inventory of assets and services deployed by the organization.
5. Rigorous, Ongoing Vulnerability Management
SaaS models bring a whole new set of vulnerabilities that enable attackers to gain unauthorized access to the infrastructure and do their bidding. So, SaaS apps and services need to be included in your organization’s rigorous, ongoing vulnerability management processes. This will help harden the security posture more effectively.
6. Integrate Real-Time Threat Detection and Protection
SaaS application security threats can be prevented by integrating real-time threat detection and protection. Using behavioral analysis, you can easily distinguish between good and bad/ malicious requests through granular traffic monitoring, preventing a whole host of known and emerging threats. It offers 24×7 visibility into the security posture in the face of the rapidly evolving threat landscape, enabling you to become proactive about security.
7. Implement a Data Retention Policy
This is important from the compliance, privacy, and data security perspectives. In drafting the data retention policies, understand what data needs to be retained and how long. Put mechanisms to delete customer data after the specified time period programmatically. Remember, non-compliance comes with exorbitant fines.
8. Stringent Access Controls
Stringent access controls based on the principles of least privileges need to be enforced for heightened SaaS security. This helps you segregate users and ensure that they get access to only necessary data for their roles within the organization. It makes it easier to monitor user-level data security.
What Are SaaS Security Best Practices?
SaaS solutions have numerous advantages for businesses, including lower initial costs, quicker deployment, scalability, and flexibility. SaaS applications include the storage and processing of sensitive data away from the direct control of the organization, which presents substantial security challenges.
Below, we’ll talk about some best practises for securing SaaS apps used by your company and defending your data against theft, loss, and unauthorized access.
1. Enhanced Authentication
Cloud providers can handle authentication in various ways, making it complicated to determine how users should be given access to SaaS resources. Some (but not all) vendors support integration with identity providers that the customer can manage, such as Active Directory (AD) with Security Assertion Markup Language, OpenID Connect and Open Authorization. Likewise, some vendors support multi-factor authentication, while others do not.
To navigate the various SaaS offerings available, it is essential that the security team understands which services are being used and the supported options for each service. This context allows administrators to choose the right authentication method (or methods) according to the organization’s needs.
A good option is to use single sign-on (SSO) tied to AD, if the SaaS provider supports it, as this ensures that the account and password policies correlate to the services in use for the SaaS application.
2. Data Encryption
The channels used to communicate with SaaS applications typically use Transport Layer Security (TLS) to protect in-transit data. Some SaaS providers also offer encryption capabilities for protecting data at rest. This could be a default feature or may need to be enabled.
Research the available security measures of each SaaS service in use to determine whether data encryption is possible and make sure to enable the encryption when relevant.
3. Oversight and Vetting
Ensure you review and evaluate any potential SaaS provider (as you would with other vendors). Make sure you understand how the service is used and which security model is used to deliver the service, as well as any available optional security features.
4. Discovery and Inventory
It is important to be able to track all SaaS usage given that usage patterns can be unexpected, especially when applications are deployed rapidly. Make sure you search for new, untracked SaaS usage and stay alert for unexpected changes.
Combine manual data collection techniques with automation tools, where possible, to keep up with rapidly evolving SaaS usage and maintain a reliable, up-to-date inventory of the services employed and who is using them.
5. CASB Tools
Consider using a Cloud Access Security Broker (CASB) solution for situations where the SaaS provider does not provide an adequate level of security. CASB allows organizations to add controls that are not included or natively supported by SaaS providers.
Explore the tools available to address any shortcomings in the SaaS provider’s security model. You should also pay attention to the different CASB deployment modes so you choose the right deployment configuration (i.e. API or proxy-based) for your organization’s architecture.
6. Situational Awareness
Monitor your SaaS use and examine the data from tools like CASBs, and keep track of the data and logs provided by the SaaS provider. IT and security executives must treat SaaS offerings differently from ordinary websites, as they are robust tools demanding the same level of security as any enterprise application.
Make sure you implement measures for systematic risk management when adopting SaaS security best practices—this helps ensure that users employ SaaS safely and that your organization’s SaaS usage remains protected.
7. Use SaaS Security Posture Management (SSPM)
SSPM ensures that SaaS applications are properly configured to protect them from compromise. Cynet provides a leading SSPM solution that continuously monitors SaaS applications to identify gaps between stated security policies and actual security posture, letting you automatically find and fix security risks in SaaS assets, and automatically prioritize risks and misconfigurations by severity.
8. Train your SaaS users
The fifth step is to train your SaaS users and raise their awareness and skills on how to use SaaS applications securely and responsibly. You should provide regular and updated security education and training programs that cover topics such as SaaS security risks, best practices, policies, and procedures.
You should also test your users’ knowledge and behavior through simulations, quizzes, or exercises, and provide feedback and guidance on how to improve. You should also foster a culture of security and accountability, and encourage your users to report any security issues or incidents that they encounter or observe.
9. Review your SaaS security
The sixth and final step is to review your SaaS security periodically and continuously and update it as needed. You should perform regular audits and assessments of your SaaS applications, providers, settings, activities, and users, and measure their performance and compliance against your security goals and standards.
You should also collect and evaluate feedback and suggestions from your stakeholders, such as your employees, customers, partners, or regulators, and incorporate them into your security improvement plans. You should also stay informed and updated on the latest SaaS security trends, threats, and best practices, and adapt your security strategy accordingly.